
1
Making the Most of Your Hard(ware) Work

Joe FitzPatrick
@securelyfitz
15+ years of hardware fun:
• silicon debug
• security research
• pen testing of CPUs
• security training
SecuringHardware.com:
• Applied Physical Attacks Training
• HardwareSecurity.Training
02
Hardwhat?




08
is harder than software
has longer development cycles
gets fewer development iterations
has real tangible costs
are riskier to deploy
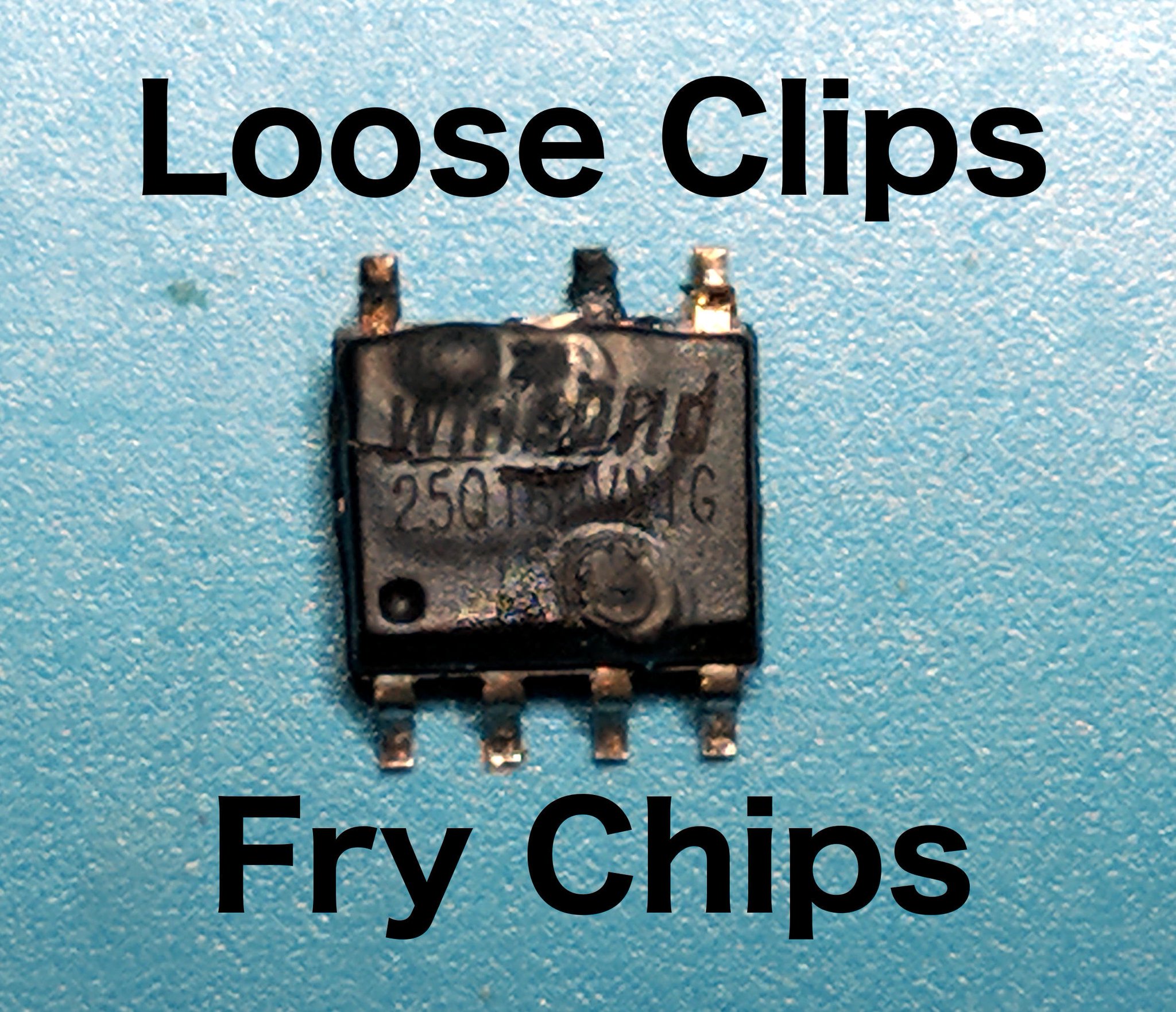
have nonzero risk of bricking
just don't scale
Ignorance to hardware vulnerabilities
General laziness (aka efficiency)
Massive *percieved* barrier to entry

14
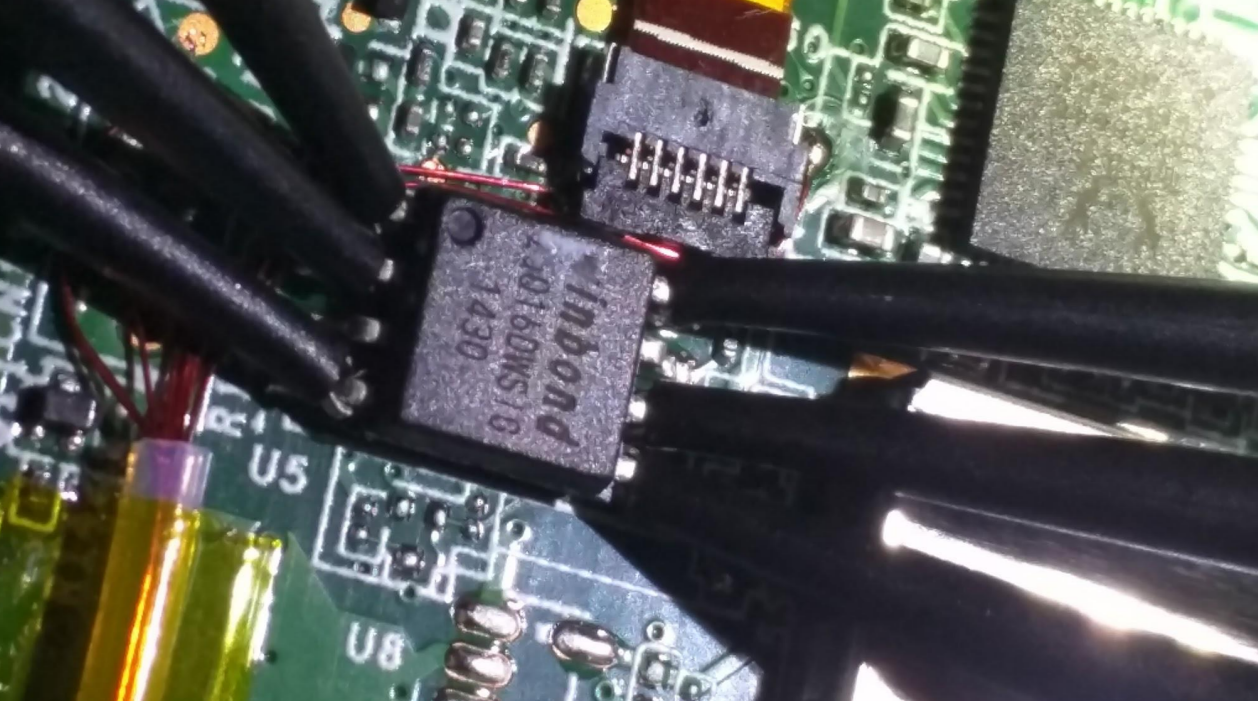
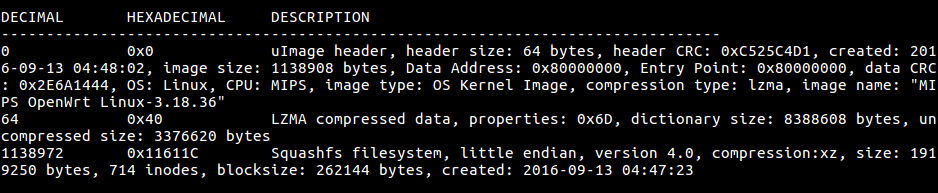
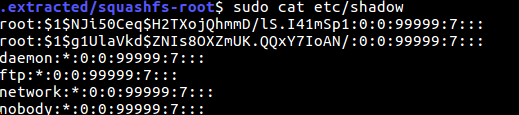
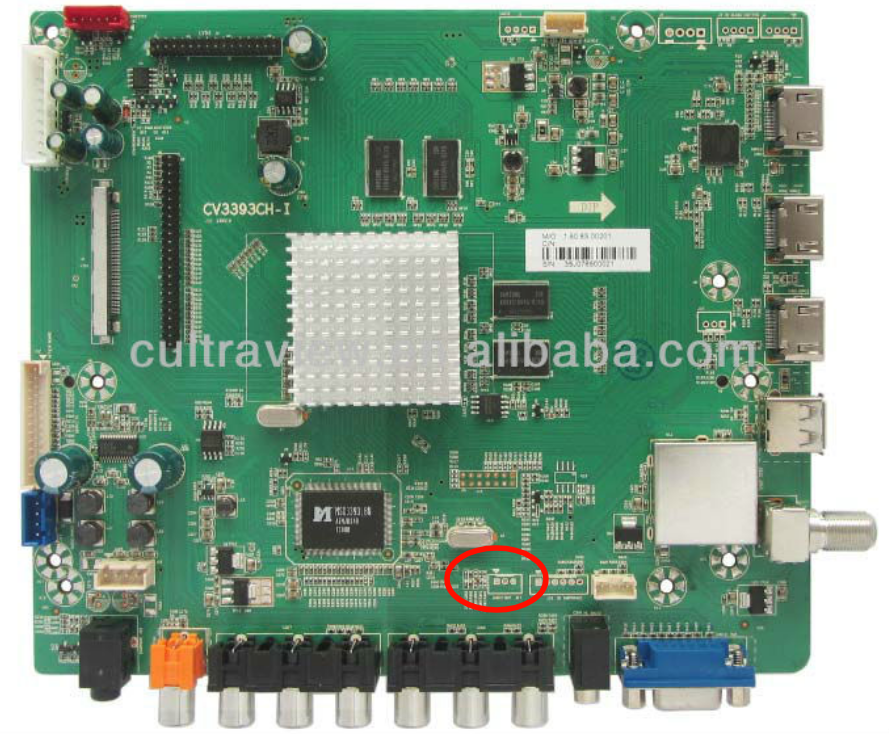
What can we do with physical access?

20
What else can we get with physical access?



26
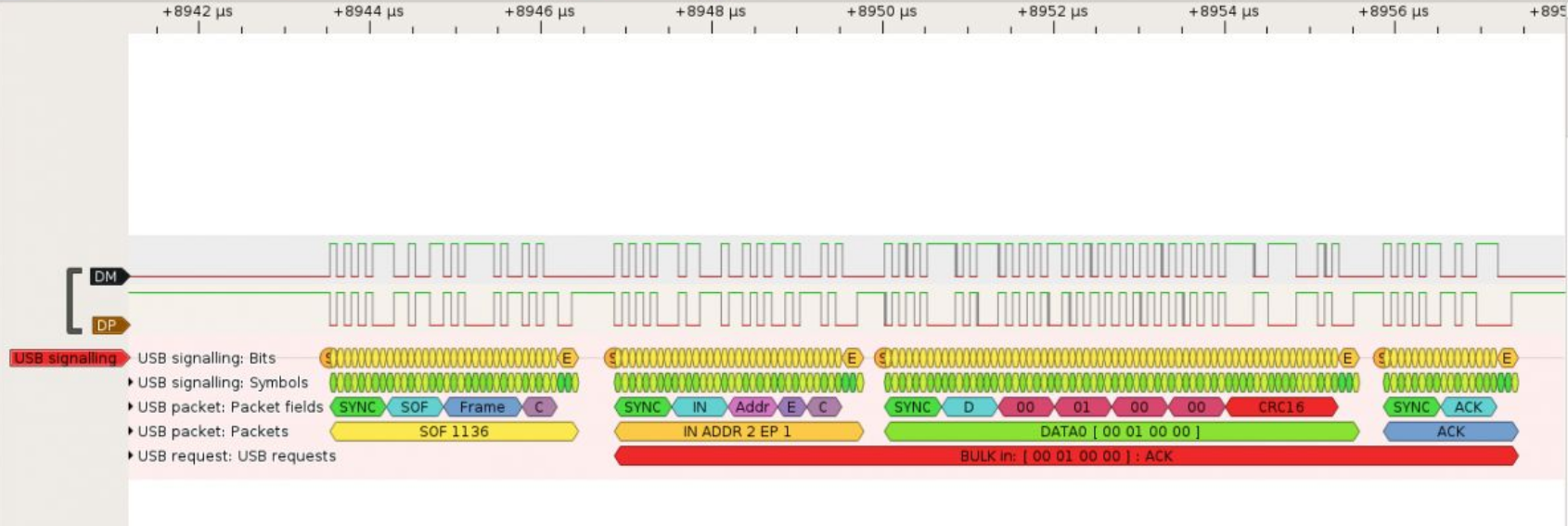
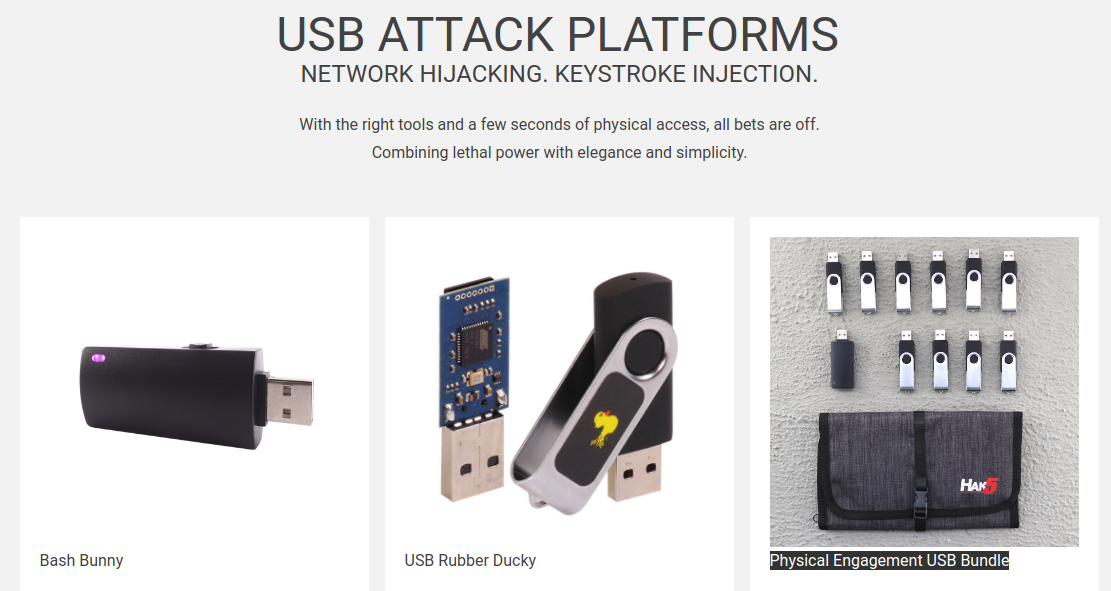
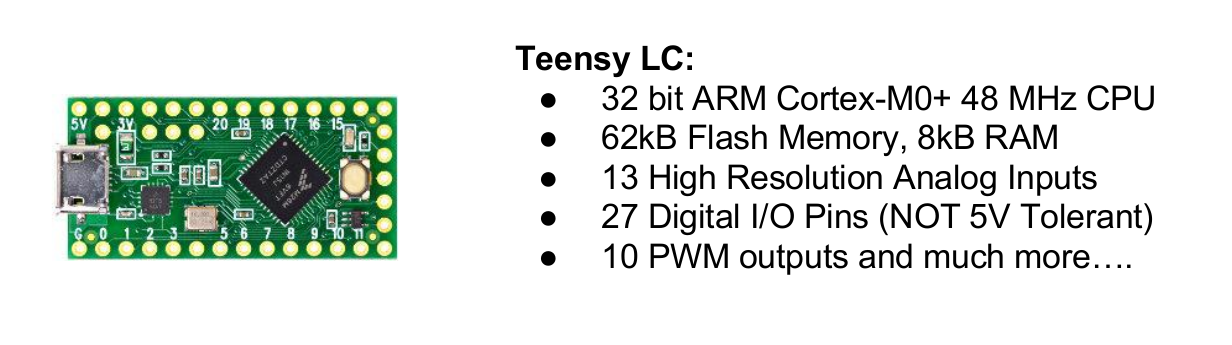
USB: Hardware Attacks with Safety Gloves On
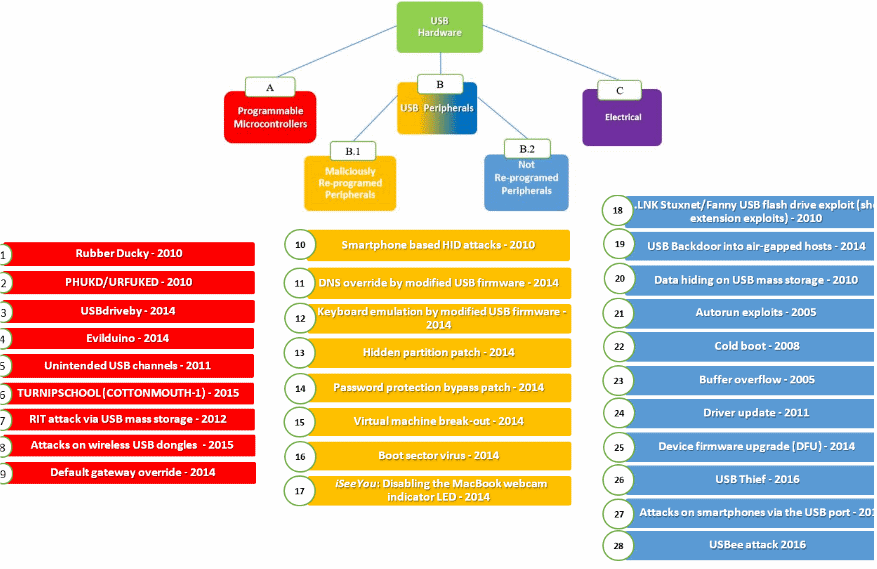
Malicious hardware device
Malicious firmware on exsiting device
Malicious payload on a normal device
Malicious electrical attacks
You'll learn more than you expect

32
Attacking the Fancy Interfaces
It's running 2.5 to 8GHz
It's locked up inside your PC
It's not like hooking wires up to a parallel port!

It automatically connects and negotiates
It has LOTS of error checking/correction
FPGAs can do it out-of-the-box*
Thunderbolt can do it too!
1. Connect everything inside your PC
2. Lock it in a box
3. Call it secure...

Think about 386 paged memory.
Think about embedded graphics.
Think about IP blocks on an SOC.
Hot swap predates thunderbolt.
Even systems that don't support hot swap - support hot swap
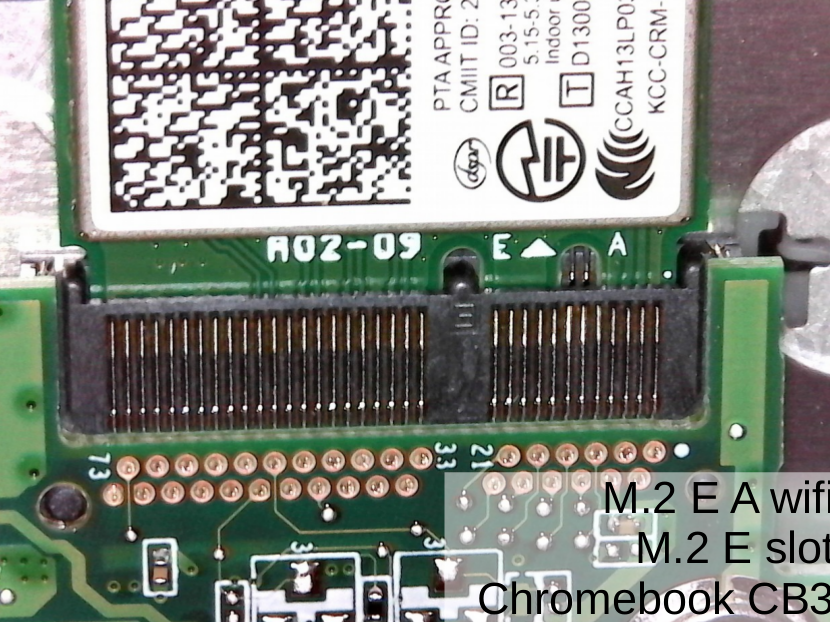
How about 3 wires:

Is an issue 'fixed' or is it just remediated?
If something seems too hard - try a different approach.
38
What can we learn about general techniques?
Step 1: Use Physical Access for a Hardware attack
Step 2: Use Hardware to escalate software privilege
Step 3: Use software privilege to do all that dirty work
Is there someone who can help me with the hardware?
Is there someone I can help with the software?
You DON'T need to do it all!
44
Harden your Hardware
50
A little bit goes a long way (for now)
Keep your expectations realistic
Get help and share what you find!
Making the Most of Your Hard(ware) Work
Joe FitzPatrick - @securelyfitz - joefitz@securinghardware.com